Mat
Mat
but i only need it for linux by now so im safe
At least w/ flatpak you're distro-independent
 Anonymous
Anonymous
 Liam
Liam
He needs no class/struct
Depends on his/her real meaning.
If he/she means not to use self-define struct, then std::tuple stands. If he/she means not to use any stuct or class, then I guess there is no known method to achieve this.
 Liam
Liam
#include <iostream>
#include <tuple>
std::tuple<bool, int> foo(bool flag, int v) {
return {not flag, flag ? ++v : --v};
}
int main() {
auto [f, v] = foo(true, 41);
std::cout << std::boolalpha << f << '\t' << v << std::endl;
return 0;
}
compile with C++17 standard, and it's looks really like Python.
 BinaryByter
BinaryByter
(And adds a new burden on stl maintainers: make sure that first is in front of second in your tuple ^^)
 Liam
Liam
but this new auto decomposition of classes is ultra cool
together with initializer list and package auto (structured bindings).
 S.
S.
 Ariana
Ariana
 Liam
Liam
Wow that's magic!
Hmmmm, suppose map is an instance of std::map<std::string, uint64_t>, then you could use
for (auto& [k, v] : map) {
...
}
 BinaryByter
BinaryByter
 Bruce
Bruce
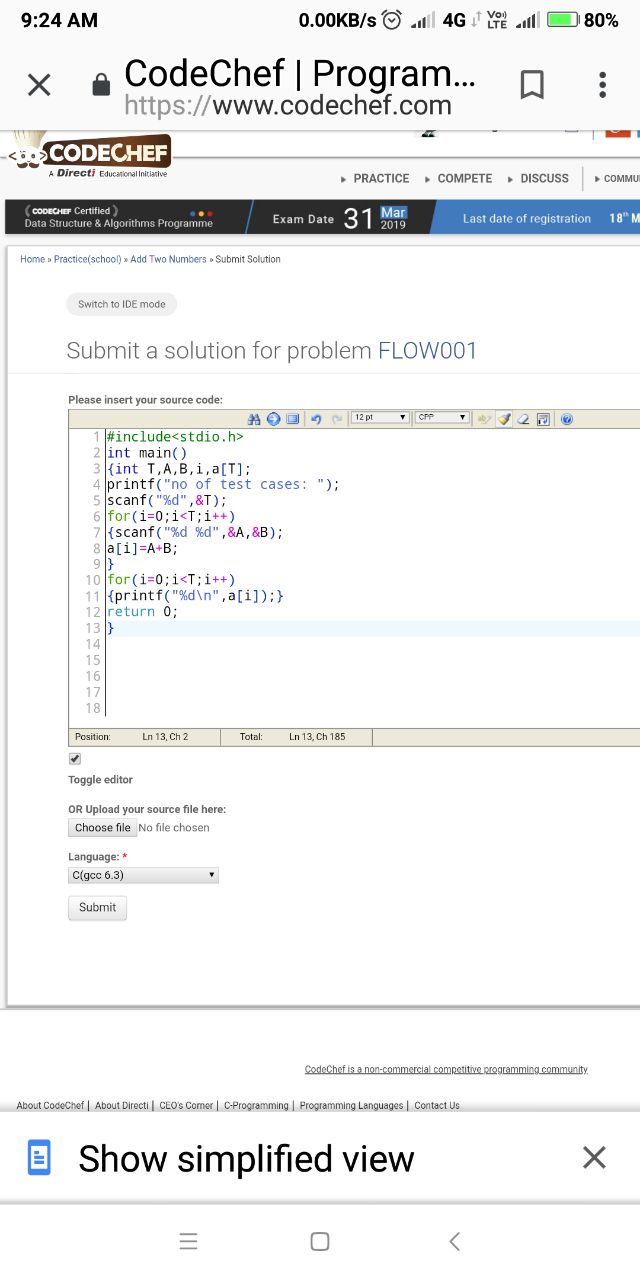
#include<stdio.h>
int main()
{int T,A,B,i,a[T];
printf("no of test cases: ");
scanf("%d",&T);
for(i=0;i<T;i++)
{scanf("%d %d",&A,&B);
a[i]=A+B;
}
for(i=0;i<T;i++)
{printf("%d\n",a[i]);}
return 0;
}
What are errors in the above code
 Anonymous
Anonymous
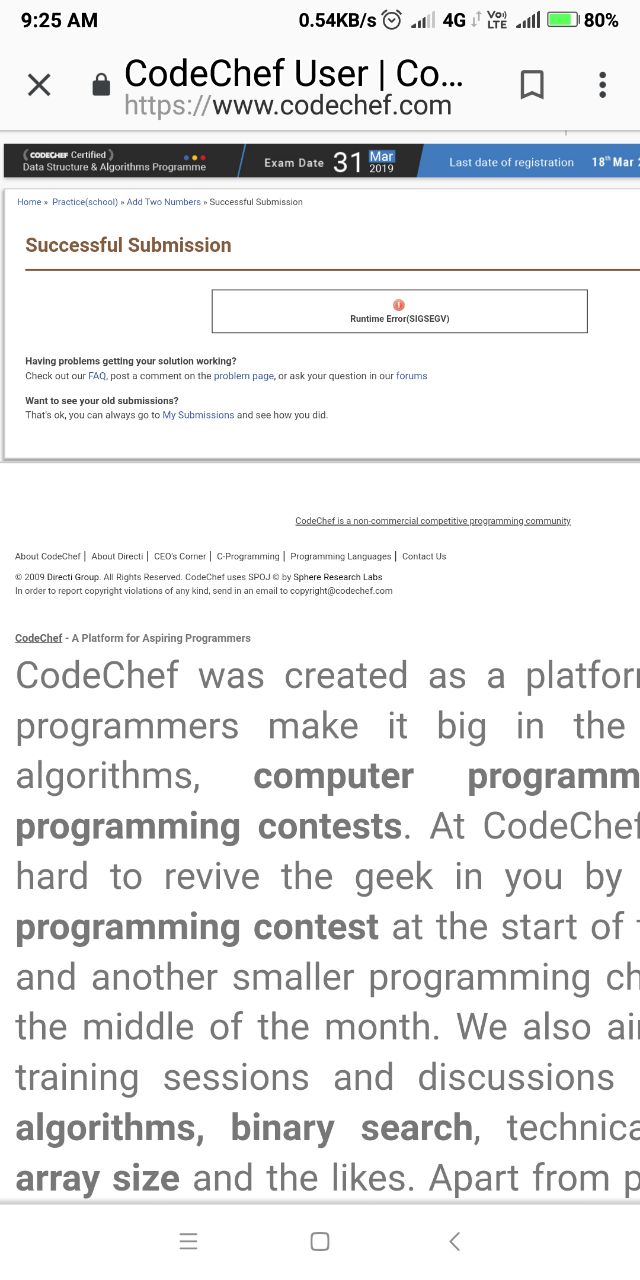
If I am not wrong, SIGSEGV is a signal for segmentation fault so that's related to incorrect memory referencing.
 Anonymous
Anonymous
C(gcc 6.3)
Maybe try copying the printf within the second loop after the assignment in the first loop
 Anonymous
Anonymous
#include<stdio.h>
int main()
{int T,A,B,i,a[T];
printf("no of test cases: ");
scanf("%d",&T);
for(i=0;i<T;i++)
{scanf("%d %d",&A,&B);
a[i]=A+B;
}
for(i=0;i<T;i++)
{printf("%d\n",a[i]);}
return 0;
}
What are errors in the above code
Two errors.. Size of array must be given when declared
Second.. Space between two %d in scanf function
 Bruce
Bruce
Maybe try copying the printf within the second loop after the assignment in the first loop
I didn't understand😕
 Anonymous
Anonymous
Two errors.. Size of array must be given when declared
Second.. Space between two %d in scanf function
For the second error you mean if the person does not enter the numbers with the space in between because I don't see why it's wrong
 Bruce
Bruce
 Bruce
Bruce
Two errors.. Size of array must be given when declared
Second.. Space between two %d in scanf function
In first error if I don't give the size the compiler is saying size must be declared
 Anonymous
Anonymous
In first error if I don't give the size the compiler is saying size must be declared
Yes but size must be a constant not a variable
 S.
S.
I done this in my mobile in website
Code Cheff so it may not be clear
It makes sense now. Just try the code on your local compiler first. You will get meaningful info
 Anonymous
Anonymous
For the second error you mean if the person does not enter the numbers with the space in between because I don't see why it's wrong
There is always a space or newline char or tab between two number
Try by removing spaces once.
 Anonymous
Anonymous
How can we declare exact size when size depends on in put T
Either by dynamic memory allocation
Or you can simply give large no say ar[1000] depending upon the constraints
 Anonymous
Anonymous
Oh hmm when I copied it over and tested it out the space was inserted between the format specifiers that's what maybe causing the issue as well.
 Liam
Liam
#include<stdio.h>
int main()
{int T,A,B,i,a[T];
printf("no of test cases: ");
scanf("%d",&T);
for(i=0;i<T;i++)
{scanf("%d %d",&A,&B);
a[i]=A+B;
}
for(i=0;i<T;i++)
{printf("%d\n",a[i]);}
return 0;
}
What are errors in the above code
Before you can figure out the size of the array a, say T, you cannot declare it.
int T, a[T];
Suppose you are your compiler, how many slots will you reserve for array a?
 Liam
Liam
With AddressSanitizer, you'll get more information about memory violation.
$ env LD_LIBRARY_PATH="/opt/gcc/gcc-8.2.0/lib64:$LD_LIBRARY_PATH" ./a.out
no of test cases: 3
1 2 3 4 5 6
=================================================================
==21038==ERROR: AddressSanitizer: dynamic-stack-buffer-overflow on address 0x7fff7264b260 at pc 0x000000400cc1 bp 0x7fff7264b230 sp 0x7fff7264b228
WRITE of size 4 at 0x7fff7264b260 thread T0
#0 0x400cc0 in main (/home/liam/test/c/a.out+0x400cc0)
#1 0x7f812573fb14 in __libc_start_main (/lib64/libc.so.6+0x21b14)
#2 0x400978 (/home/liam/test/c/a.out+0x400978)
Address 0x7fff7264b260 is located in stack of thread T0
SUMMARY: AddressSanitizer: dynamic-stack-buffer-overflow (/home/liam/test/c/a.out+0x400cc0) in main [0/3848]
Shadow bytes around the buggy address:
0x10006e4c15f0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10006e4c1600: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10006e4c1610: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10006e4c1620: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10006e4c1630: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x10006e4c1640: 00 00 00 00 00 00 00 00 ca ca ca ca[cb]cb cb cb
0x10006e4c1650: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10006e4c1660: f1 f1 f1 f1 04 f2 f2 f2 f2 f2 f2 f2 04 f2 f2 f2
0x10006e4c1670: f2 f2 f2 f2 04 f2 f2 f2 f3 f3 f3 f3 00 00 00 00
0x10006e4c1680: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10006e4c1690: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==21038==ABORTING
 Anonymous
Anonymous
I'm able to run his code without error on gcc8. I think they msut be using dynamic memory allocation of some sort.
 Liam
Liam
Check this line:
0x10006e4c1640: 00 00 00 00 00 00 00 00 ca ca ca ca[cb]cb cb cb
ca means memory before actually allocated, and cb means memory after actually allocated. As you can see, since you allocate a[T] before T is correctly initialized, it's zero, and hence the size of a is zero (`cb`s is exactly after `ca`s).
When you are trying to write something in `a[0], the sanitizer detects that you are trying to dereference `cb, and reports the error.
 Liam
Liam
I'm able to run his code without error on gcc8. I think they msut be using dynamic memory allocation of some sort.
No. It's undefined behavior. No runtime error doesn't mean the code is correct.
 Anonymous
Anonymous
No. It's undefined behavior. No runtime error doesn't mean the code is correct.
Yeah gcc can hide the errors sometimes
 Anonymous
Anonymous
Can you try initializing the array after the input is entered into T?
Anyways I also suggested him to try the same thing at first
 BinaryByter
BinaryByter
I done this in my mobile in website
Code Cheff so it may not be clear
coding on a phone is eww
 Liam
Liam
Yeah gcc can hide the errors sometimes
It's not GCC...
Check this code:
#include <stdio.h>
int main() {
int before1 = 0;
int before2 = 0;
int a[0];
int after1 = 0;
int after2 = 0;
printf("before: %d %d, after: %d %d.\n", before1, before2, after1, after2);
a[0] = 42;
printf("before: %d %d, after: %d %d.\n", before1, before2, after1, after2);
return 0;
}
I declared an array of int of size 0, and a out-of-boundary write happened after that a[0] = 42;.
The result might be:
before: 0 0, after: 0 0.
before: 0 0, after: 0 42.
See? There might be no run time error, but the result of the program is wrong. As you could see, after2 is modified unexpectedly to 42.
 Parra
Parra